New PoPS Border Simulation Supports Front Lines of Pest Detection
UPDATE: May 12, 2022 –– The first peer-reviewed paper using the PoPS Border simulation (v 1.0.2) was published today in the international journal Risk Analysis:“Contaminated consignment simulation to support risk-based inspection design“
Developers at the Center for Geospatial Analytics at North Carolina State University have released new software to inform border inspections for insect pests and plant disease at ports of entry. The release, PoPS Border 1.0, is the newest in the Pest or Pathogen Spread (PoPS) suite of models developed at the Center.
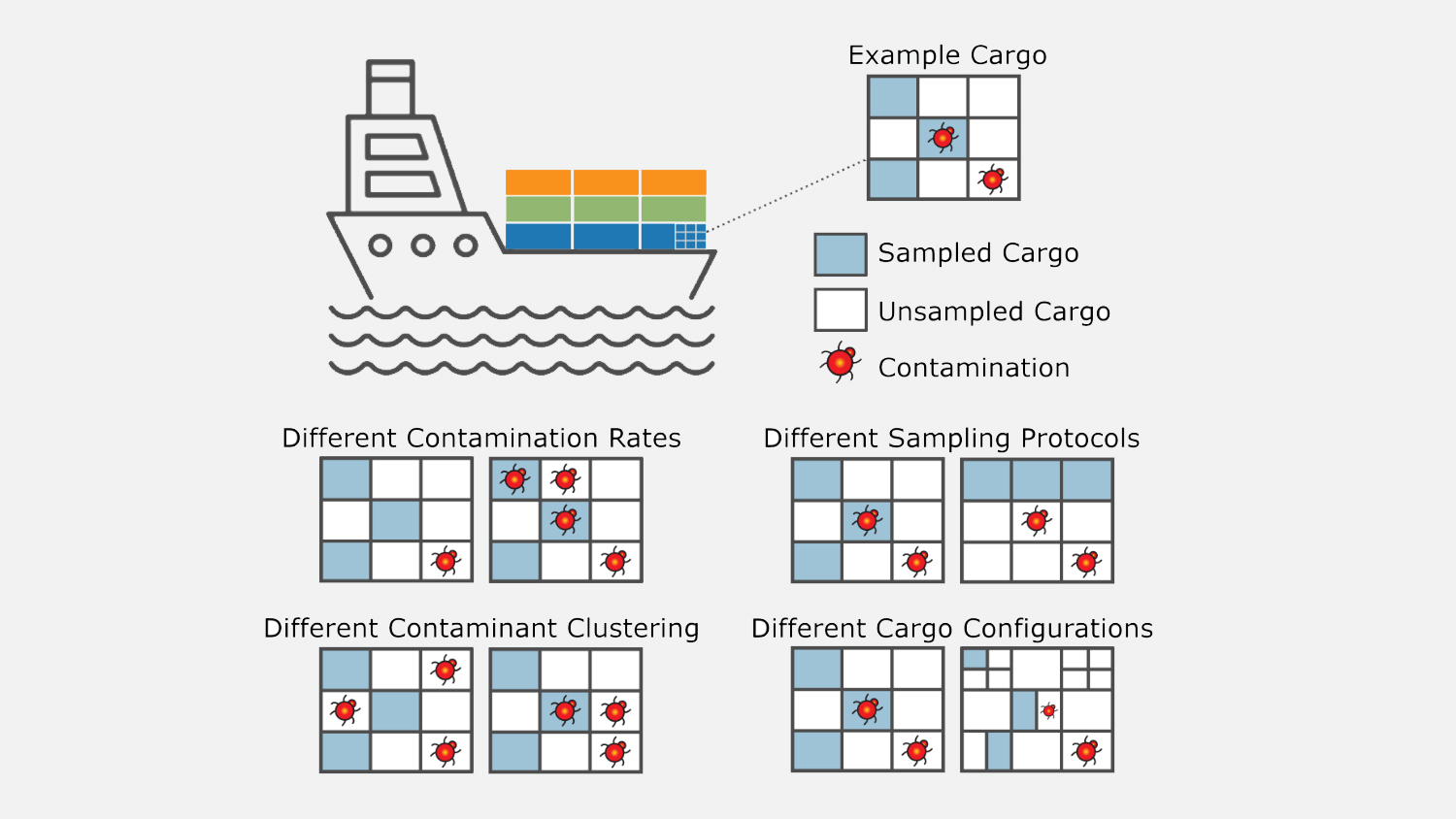
PoPS Border simulates the outcomes of border inspections––that is, how many pests in a shipment are missed versus detected––depending on user-specified inputs such as shipment size, packaging type, levels and arrangement of pest contamination, and inspection protocol (sample size and selection).
The simulation can be used to assess hypothetical scenarios of shipment contamination or can be based on records from real ports, using known sampling methods and pest detections to determine the potential for pests to slip through unnoticed.
Measurements of undetected pests are “very valuable and difficult to come by for biological invasions research in general,” explains Kellyn Montgomery, lead researcher of the PoPS Border project and recent graduate of the Geospatial Analytics Ph.D. program; she and Geospatial Research Software Engineer Vaclav Petras developed the PoPS Border code.
PoPS Border “fills a big need, a gap, that phytosanitary agencies have,” Montgomery says. Border inspection agents operate in a fast-paced environment, under constant pressure to keep the flow of commerce moving. “They are constantly confronted with changing conditions and it can be difficult to measure the impact of their decisions,” she explains.
The PoPS Border simulation, meanwhile, allows analysts to “conduct experiments that you really can’t do in an operational environment,” Montgomery says. It “provides an environment where you can test…combinations of factors” that influence how well an inspection protocol performs.
For example, PoPS Border can identify scenarios in which different protocols optimally balance available resources, inspection effort and pest detection. In situations where required effort would outstrip capacity, PoPS Border can help with “designing alternative strategies that reduce workload and are still effective for intercepting pests,” Montgomery explains.
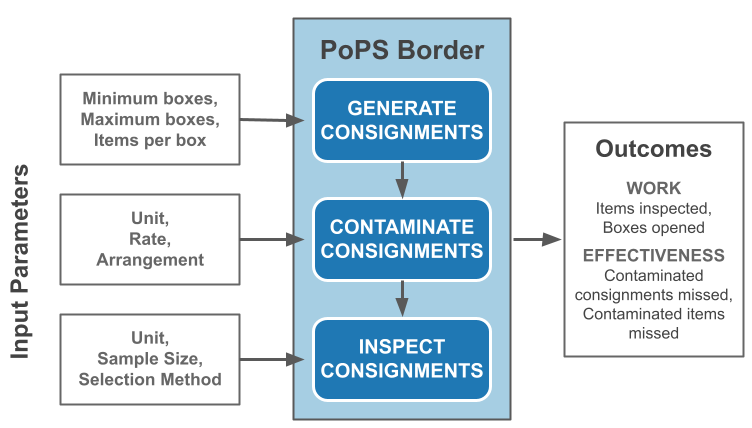
“What-if” experiments conducted with PoPS Border can quantify the effectiveness of different inspection protocols under varying conditions, as well as provide a mechanism for “estimating how many pests are making it past inspection,” Montgomery says.
Measurements of missed detections can then inform spread simulations, like PoPS 1.0 released last year, by quantifying propagule pressure, or the number of individuals of a potentially invasive species introduced to an area. “Propagule pressure is usually measured with a proxy like trade,” Montgomery explains, but PoPS Border estimates pest numbers with greater specificity by considering variable contamination rates and missed detections from that trade.
The PoPS Border simulation is flexible, open source and can be broadly applied beyond border protection to other quality assurance or inspection scenarios. It was developed based on inspection methods used in the United States but can be expanded for international use as well.
“The ideal case would be if someone extended the open source project we established by adding country-specific inspection methods we haven’t included yet,” says Petras.
“Any addition someone would make would be useful to all users,” Montgomery adds.
To get started, users can follow the tutorials and installation instructions provided in the PoPS Border README file.


